|
Mittwoch, 22. Juni 2005
PiNg_TrAcErT
rene.hofer.uni-linz, 21:07h
PING mit msdos:+++++++++++++++++++++++++++++++++++mittwoch, 22_06_2005_2050:+++++++++++++++++++++++++++++++++++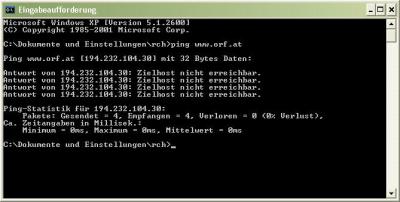 +++++++++++++++++++++++++++++++++++ sonntag, 26_06_2005_1130:+++++++++++++++++++++++++++++++++++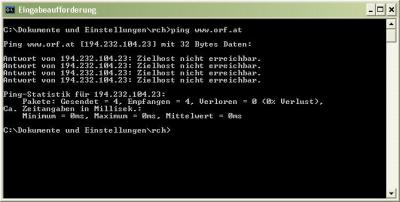
INTERPRETATION:ping ergab, dass alle gesendeten Pakete zurückkamen, jedoch ohne Angabe von round-Zeiten. Diese wären für eine Interpretation interessant! Dies ist meiner Meinung nach darauf zurückzuführen, dass die Firewall(s) der orf-Server den ping-Befehl nur eingeschränkt zulassen. Anzumerken sei hier noch, dass die Server des ORF natürlich (aufgrund des hohen Zugriffsvolumens) mehrere öffentliche IP-Adressen haben. So wurde am Mittwoch zB 194.232.104.30, am Sonntag 194.232.104.23 angesprochen. Stichwort 'verteilte Systeme'.TRACERT mit msdos:+++++++++++++++++++++++++++++++++++mittwoch, 22_06_2005_2050:+++++++++++++++++++++++++++++++++++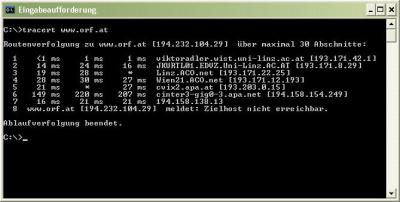 +++++++++++++++++++++++++++++++++++ sonntag, 26_06_2005_1130:+++++++++++++++++++++++++++++++++++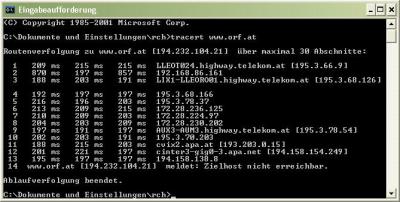
INTERPRETATION:Ebenso wie bei ping, ergibt tracert eine Firewall-Aktivität. Die Route lässt sich zwar de facto bis zum ORF-Server verfolgen, dieser lässt jedoch den Befehl an sich nicht durch die Firewall. Da der ORF-Server jedoch am Ende der Kette steht, ist eine Verfolgung de facto doch möglich.Was die Zeiten betrifft, so ist zu vermerken, dass am Wochenende die Server nicht so schnell reagieren wie unter der Woche. Grund dafür dürften die vielen privaten user sein, die im Internet unterwegs sind. Anmerkung des Autors: Die pings, tracerts wurden am Sonntag von einem anderen Internetanschluss durchgefüht, als am Mittwoch (wie unschwer zu erkennen ist). TRACERT mit webtool von UTA:+++++++++++++++++++++++++++++++++++mittwoch, 22_06_2005_2050:+++++++++++++++++++++++++++++++++++Ergebnis: traceroute to www.orf.at 1 fwsrv1.ces.uta.at (213.90.2.2) 0.514 ms 0.207 ms 0.421 ms 2 213.90.1.17 (213.90.1.17) 1.345 ms 0.720 ms 0.797 ms 3 wat1-15-21.net.uta.at (62.218.15.21) 1.489 ms 0.605 ms 0.824 ms 4 c76vix1-g4-2.net.uta.at (212.152.192.105) 1.506 ms 1.818 ms 1.701 ms 5 cvix1.apa.net (193.203.0.5) 1.518 ms 1.904 ms 1.731 ms 6 cinter1-gig0-3.apa.net (194.158.155.101) 2.397 ms 2.789 ms 2.147 ms 7 194.158.138.12 (194.158.138.12) 2.431 ms 4.459 ms 3.014 ms 8 www.orf.at (194.232.104.30) 3.314 ms !<10> 2.414 ms !<10> 3.030 ms !<10> +++++++++++++++++++++++++++++++++++ sonntag, 26_06_2005_1130:+++++++++++++++++++++++++++++++++++1 fwsrv1.ces.uta.at (213.90.2.2) 0.871 ms 0.436 ms 0.396 ms 2 213.90.1.17 (213.90.1.17) 1.510 ms 2.264 ms 1.831 ms 3 wat1-15-21.net.uta.at (62.218.15.21) 0.713 ms 0.823 ms 0.882 ms 4 c76vix1-g4-2.net.uta.at (212.152.192.105) 1.654 ms 1.831 ms 1.841 ms 5 cvix1.apa.net (193.203.0.5) 2.626 ms 1.769 ms 1.824 ms 6 cinter1-gig0-3.apa.net (194.158.155.101) 1.638 ms 2.822 ms 2.294 ms 7 194.158.138.11 (194.158.138.11) 3.103 ms 2.380 ms 3.739 ms 8 www.orf.at (194.232.104.25) 5.975 ms !<10> 6.846 ms !<10> 5.193 ms !<10> INTERPRETATION:Der Unterschied zum Windows-tool liegt darin, dass beim webtool vom UTA-server ausgegangen wird, dh die Adresse des UTA-Servers (213.90.2.2) das tracert absendet und nicht der eigene Rechner!PORTSCAN mit webtool:+++++++++++++++++++++++++++++++++++
INTERPRETATION:Durch die bewusste Verwendung und vor allem RICHTIGE KONFIGURATION einer Firewall können Angriffe von außen verhindert werden. In meinem Fall gibt es bei den obigen ports (Anmerkung: und auch nicht bei anderen) nicht einmal die Möglichkeit für einen anderen Internetuser, sich auf meinem Rechner ports zunutze zu machen, da diese erst gar nicht sichtbar sind.... comment |
Online for 7380 days
Last update: 2005.06.26, 12:12 You're not logged in ... login
PiNg_TrAcErT
PING mit msdos: ++++++++++++++++++++++++++++++++++ by rene.hofer.uni-linz (2005.06.26, 12:12) gute darstellung
gelungene Darstellung der Kennzeichnung von Daten!... by Martin.Klaushofer.Uni-Linz (2005.06.15, 10:51) DRM - Digital Rights...
Zu Beginn dieser story möchte ich gleich auf einen... by rene.hofer.uni-linz (2005.06.14, 22:36) Sicherheit im Internet
Ich finde das sehr gut wie du das in deinem Beitrag... by Andrea.Muehlsteiner.uni-linz (2005.05.10, 22:49) E-Mails - Verschlüsselung
Private emails braucht man mit Sicherheit oftmals nicht... by rene.bolz.uni-linz (2005.05.10, 19:16) |
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||